Security operations for modern infrastructure
across logs, network, and endpoints
Unified visibility. Real-time correlation. Flexible deployment.
Designed for reliability, control, and scale.
Platform capabilities
Everything you need for detection and investigation — in one platform.
Network Detection
Identify threats traversing your network in real time using deep packet inspection and protocol analysis. BluScout monitors all types of traffic to surface suspicious patterns, lateral movement, and command-and-control(C2) activity before damage is done.
Network Performance Monitoring
Gain visibility into network health and performance alongside security telemetry. Track latency, throughput, retransmissions, and protocol errors to distinguish between operational issues and security events, all from the same platform.
Network Forensics
Reconstruct network sessions and examine protocol level details to support post incident investigations. Capture and analyze full packet data to determine exactly what happened, what was exfiltrated, and how the attacker moved through your environment.
Log Management
Collect, parse, and retain logs from across your infrastructure with extensible parsing and policy driven retention. Normalize diverse formats into a unified schema so every log source is searchable, correlated, and audit-ready from day one.
Detection & Correlation
Apply detection rules across logs, network, and endpoint telemetry with real-time correlation. Link related events into higher confidence alerts to reduce noise and surface the activity that matters most to your security operations.
Endpoint Monitoring
Monitor process execution, file system changes, and system activity on Windows and Linux endpoints. Capture the endpoint context needed to detect malware behavior, privilege escalation, and persistence techniques across your environment.
Threat Detection
Leverage curated threat intelligence feeds and detection content to identify known and emerging threats. Enrich alerts with indicator context and map detections to attacker techniques for faster prioritization and response.
Incident Investigation
Pivot seamlessly across logs, packets, and endpoint data with unified search and timeline reconstruction. Build complete incident timelines from initial access to impact, reducing mean time to understand and accelerating root cause analysis.
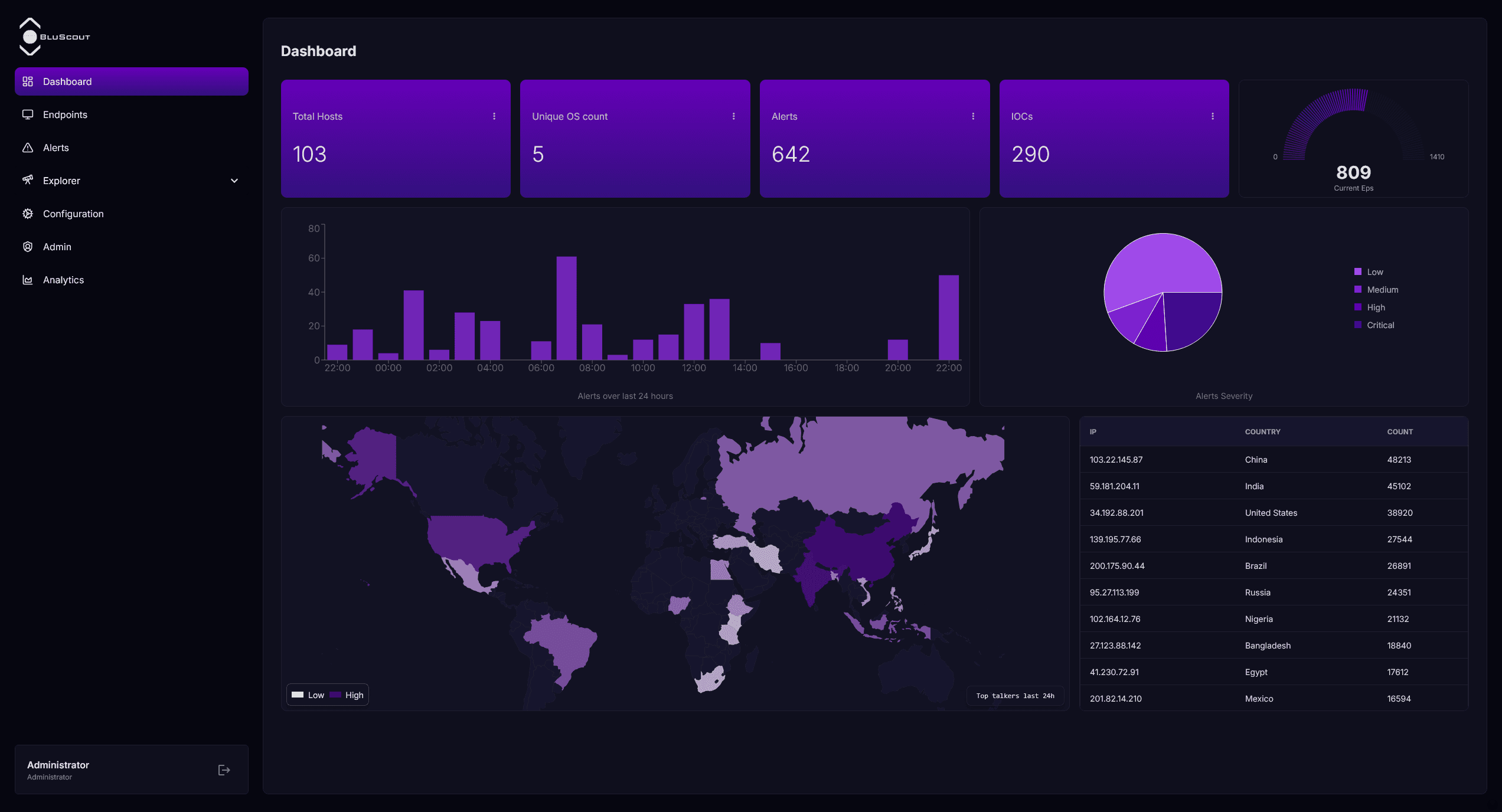
Designed for security operations
A consistent workflow from detection to investigation to day-to-day operations.
Detect
Centralize telemetry and apply detections that evolve with your environment without operational interruptions.
- Real-time correlation across logs, packets, and endpoints
- Custom and curated detection rules
- Threat intelligence enrichment for higher confidence alerts
- Configurable alerting and escalation paths
Investigate
Pivot across data sources with shared context to accelerate triage and root cause analysis.
- Unified search across all telemetry types
- Timeline reconstruction from initial access to impact
- Full packet capture and session reconstruction
- Contextual pivoting between related events
Operate
Maintain governance, retention, and deployment controls that scale with your organization.
- Role based access control and audit trails
- Policy driven log retention and storage
- Cloud, on-premise, and hybrid deployment
- Extensible parsing for any log source
Legacy SIEM approaches vs BluScout
A modern approach to visibility, correlation, and operational control across environments.
Ready to see BluScout in action?
Tell us about your environment and we'll show you how BluScout maps to your telemetry, retention, and deployment requirements.